Test-driven development TDD implementation
The fifth testing principle states that a variety of tests and techniques should be used to expose a range of defects across different areas of the product. Once the causes are identified, efficient test managers are able to focus testing on the sensitive areas, while still searching for errors in the remaining software modules. Debugging is a part of the development activity that identifies, analyzes, and removes defects. Now that we have established the need for software testing let us list some common software testing terms in the following section. However, every mistake does not lead to a defect, neither does every defect lead to a failure. Sometimes, defects lie dormant within the software till they are triggered.

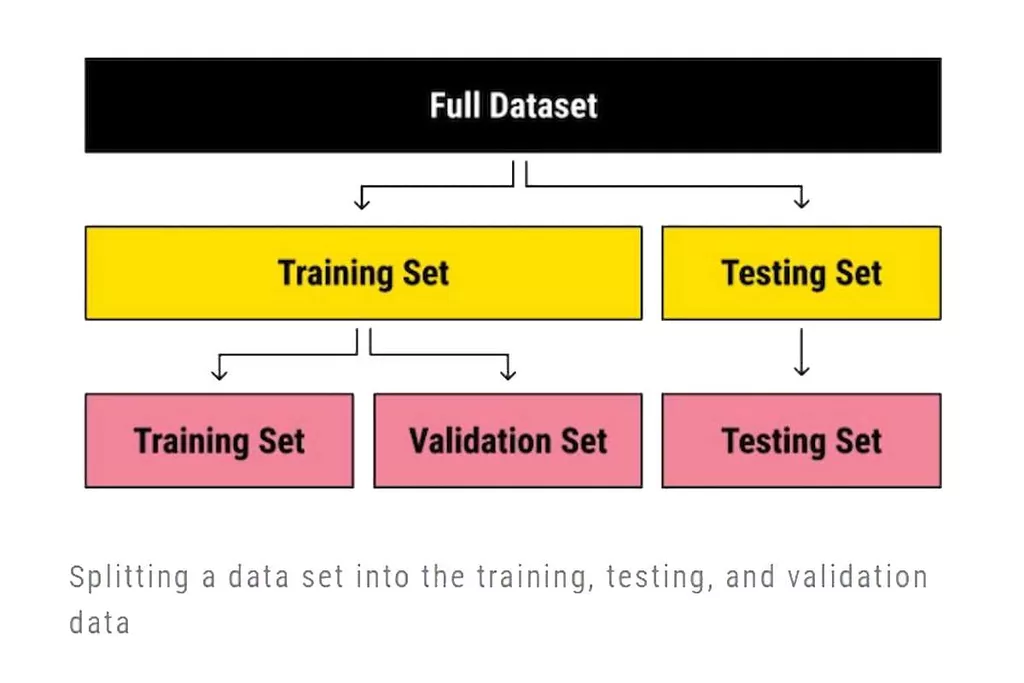
By spending a little more time on the front end of the SDLC, it’s possible to shorten the full SDLC significantly. Additionally, TDD improves the quality of software releases, which can lead to higher customer satisfaction and more revenue. Before writing a test case, QA engineers and testing team members should first determine the scope and purpose of the test.
Software Testing Process
If one module misbehaves in a chain of interrelated modules, it is not so immediately clear where to look for the cause of the failure. With ATDD, the development team now has a specific target to satisfy – the acceptance tests – which keeps them continuously focused on what the customer really wants from each user story. However, it is important to remember that although large portions of the organization may be stressed during the testing process, the whole organization would suffer if a faulty ERP system went into production. Similarly, acceptance of its functionality by cross sections of end users can give the implementation team the confidence that their system, as designed, will deliver for the business. Test cases define what must be done to test a system, including the steps executed in the system, the input data values that are entered into the system and the results that are expected throughout test case execution.
The @ character separates the dependency’s coordinates from the artifact’s file extension. When you declare a dependency or a dependency constraint, you can provide a custom reason for the declaration. This makes the dependency declarations in your build script and the dependency insight report easier to interpret. You can declare a dependency on the API of the current version of Gradle by using the DependencyHandler.gradleApi() method. This is useful when you are developing custom Gradle tasks or plugins.
Performance Testing in the Age of Agile
Major enterprises rely on Perfecto for all types of testing — especially types of automation testing. We love helping development and testing teams reach fully scaled and optimized DevOps without compromising quality. With Perfecto, your test automation and continuous testing will reach maximum elevation. Manual testing is the most hands-on type of testing and is employed by every team at some point. Of course, in today’s fast-paced software development lifecycle, manual testing is tough to scale. This type of non-functional software testing process determines how the software application behaves while being accessed by multiple users simultaneously.
- From planning and research to execution and maintenance, every phase plays a crucial role in testing a product.
- To implement TDD successfully, management cannot allow elitist and speed-at-all-costs attitudes to persist.
- It is performed by the software developer or engineer during the construction phase of the software development life cycle.
- The user experience is directly proportional to the quality of a product.
There are many testing frameworks and tools that are useful in TDD. Use a complete test management platform with integrated issue tracking. On the other hand, a test case describes the idea that is to be tested; it does not detail the exact steps to be taken. Therefore, test scripts are more detailed testing documents than test cases, but test cases are more detailed than test scenarios.
What are the benefits of adopting TDD?
By the 1980s, development teams looked beyond isolating and fixing software bugs to testing applications in real-world settings. It set the stage for a broader view of testing, which encompassed a quality assurance process that was part of the software development life cycle. Unit testing is a software development process that involves a synchronized application of a broad spectrum of defect prevention and detection strategies in order to reduce software development risks, time, and costs.
And then for each bug you fix, it would be wise to check that they don’t get back in newer releases. Automation is key to make this possible and writing tests sooner or later will become part of your development workflow. Performance tests evaluate how a system performs under a particular workload.
By increasing customer satisfaction, you’ll enjoy an increased ROI and improved brand presence. Activities in this phase include brainstorming for requirement analysis and identifying and prioritizing test requirements. They also include picking out requirements for both automated and manual testing. There are a few things you have to test even if not explicitly mentioned. A click on an active button should do something, a text field for phone number shouldn’t accept alphabets submitted. In the previous section, we saw that the end goal of SDLC is to deploy high-quality products.
Once the discrepancies have been fixed, repeat test activities to verify whether the fix has resolved them. For differences between actual and expected results, report discrepancies implementation testing as incidents. If the requirement is specified as “the software needs to respond quickly,” it is not testable, as “quick” can be interpreted in more than one way.
- Published in Software development
What Is C++? A Complete Introduction To C++ Programming Unstop formerly Dare2Compete
C++, also popularly known as ‘C with classes’, has evolved and diversified a lot over the course of time and is implemented as a compiled language. There are lots of definitions of “object oriented”, “object-oriented programming”, and “object-oriented programming languages”. For a longish explanation of what Stroustrup thinks of as “object oriented”, read Why C++ isn’t just an object-oriented programming language. That said, object-oriented programming is a style of programming originating with Simula (about 40 years ago!) relying on encapsulation, inheritance, and polymorphism. Originally developed by James Gosling at Sun Microsystems , Java is one of the most diverse languages of today’s time. Used by hundreds of Software Companies and millions of developers all around the globe, Java has become the most popular language which is used to build software applications to solve real-world problems.
- Thus, C++ allows fast compilation and execution of applications.
- The whole time that Mozilla Firefox is being made, C++ is used.
- Memory is allocated for objects, while classes don’t take up memory.
- C programming is using the language known as C to write source code, which is then compiled into programs.
- And before jumping on the comparison of C vs C++, we should read about the features of both of them as well.
- C++ was first released in 1985 as an evolution of C; ever notice the genius behind the name as we use ‘++’ to increment variables in C languages?
Similarly, the order of evaluation of arguments is unspecified. Because machines differ and because C left many things undefined. For details, including definitions of the terms “undefined”, “unspecified”, “implementation defined”, and “well-formed”; see the ISO C++ standard. Note that the meaning of those terms differ from their definition of the ISO C standard and from some common usage. You can get wonderfully confused discussions when people don’t realize that not everybody shares definitions.
The Best Tutorials for Learning C and C++
Arguably, it’s the best way to learn C++ as your first language. Also, if you find game development interesting, this is a good first course to take. This comprehensive C programming online course is great for beginners. It starts with the basics of C and programming in general, and covers advanced topics, such as dynamic memory allocation and file management. As a low-level language, C++ can closely communicate and work with hardware resources.

A standards committee operating under the auspices of the International Organization for Standardization formed shortly thereafter in 1991, and it standardized C++ in 1998 with the update C++98. Another update followed in 2003, when C++ was the most-looked-for language on Web search engines. As mentioned above, the STL is a collection of templates of wide range of generic algorithms and iterators. It includes algorithms like searching, sorting, and manipulating sequences. The Boost C++ Libraries- This comprises a set of open-source libraries that extend the functionality of C++. Our C++ tutorial is designed for beginners and professionals.
Q.2: How are C and C++ different?
In 1985, the first edition of The C++ Programming Language was released, which became the definitive reference for the language, as there was not yet an official standard. The first commercial implementation of C++ was released in October of the same year. In 1984, Stroustrup implemented the first stream input/output library. The idea of providing an output operator rather than a named output function was suggested by Doug McIlroy .
With OO and generic programming, reuse can also be accomplished by having old code call new code. For example, a programmer might write some code that is called by a framework that was written by their great, great grandfather. In fact, for dynamic binding with virtual functions, it doesn’t even need to be recompiled. Even if all you have left is the object file and the source code that great-great-grandpa wrote was lost 25 years ago, that ancient object file will call the new extension without anything falling apart. The coding language first made its appearance in the programming world in 1979. And today, it is one of the most versatile programming languages used for a wide variety of applications.
C++ is an Object-oriented supported language
C++ falls into this category because it supports several paradigms. It’s not an exclusively object-oriented language, but a functional and procedural language as well. Object-oriented programming is one of the most popular programming paradigms. The C++ programming language is one of many languages that supports object-oriented programming, alongside Java, C#, Python, and JavaScript. Some developers consider C++ to be an object-oriented language, while others argue that it’s not. Today, we’ll discuss object-oriented programming to understand whether C++ is an object-oriented programming language.

Perhaps you’d prefer more structure and a defined timeline? In that case, a C++ boot camp could be an excellent option. These are usually focused environments that get you up to speed very quickly, and they often include a capstone project and a certificate of completion. Fast approaching the age of 40, the C++ language remains one of the most popular, with more than 27% of developers surveyed in 2022 making it their language of choice. Great Learning’s Blog covers the latest developments and innovations in technology that can be leveraged to build rewarding careers. You’ll find career guides, tech tutorials and industry news to keep yourself updated with the fast-changing world of tech and business.
What is the difference between C++98 and C++11?
It is the fourth most popular programming language in the world right now, according to InfoWorld. C++ has been around for a long time even though other languages have been updated or replaced by newer, better ones. This is mostly because the original version is constantly being updated and improved. Over the last 10 years, these changes have been happening all the time, with major new releases and additions to the standard library happening in 2011, 2014, and this year. Compiling file1.c and file2.c and linking the results into the same program is illegal in both C and C++. A linker could catch the inconsistent definition of S, but is not obliged to do so (and most don’t).
It is hence often used in scientific research and computation. C++ is a middle-level language, as it encapsulates both high and low level language features. C++ is one of the predominant languages for the development of all kind of technical and commercial software. These are some of the key points to keep in mind when working with C++. By understanding these concepts, you can make informed decisions and write effective code in this language. C++ is a commonly-used language for flight software that powers commercial airplanes and military and defense aircraft (such as the F-16 and F-35 planes).
Embedded Systems & IoT
When Stroustrup invented C++, he wanted C++ to be compatible with a complete language with sufficient performance and flexibility for even the most demanding systems programming. He “had a perfect dread of producing yet-another pretty language with unintentional limitations.” See Section 2.7 of The Design and Evolution c++ software development of C++ for historical details. Companies successfully teach standard industry “short courses,” where a university semester course is compressed into one 40 hour work week. The most widely circulated comparisons tend to be those written by proponents of some language, Z, to prove that Z is better that other languages.
Various embedded systems like medical machines, smartwatches, etc., use C++ as the primary programming language. There are probably tens of thousands, if not millions of different tools across all the programming languages. A class containing a pure virtual function is called an abstract class. Objects cannot be created from an abstract class; https://globalcloudteam.com/ they can only be derived from. Any derived class inherits the virtual function as pure and must provide a non-pure definition of it before objects of the derived class can be created. A program that attempts to create an object of a class with a pure virtual member function or inherited pure virtual member function is ill-formed.
- Published in Software development
Chapter 8 Expression syntax in test scenarios Red Hat Process Automation Manager 7.4 Red Hat Customer Portal
Functional testing within OAT is limited to those tests that are required to verify the non-functional aspects of the system. Component interface testing is a variation of black-box testing, with the focus on the data values beyond just the related actions of a subsystem component. The practice of component interface testing can be used to check the handling of data passed between various units, or subsystem components, beyond full integration testing between those units. The data being passed can be considered as “message packets” and the range or data types can be checked, for data generated from one unit, and tested for validity before being passed into another unit. One option for interface testing is to keep a separate log file of data items being passed, often with a timestamp logged to allow analysis of thousands of cases of data passed between units for days or weeks. Tests can include checking the handling of some extreme data values while other interface variables are passed as normal values.

Output videos are supplemented by real-time tester input via picture-in-a-picture webcam and audio commentary from microphones. Static testing involves verification, whereas dynamic testing also involves validation. Outsourcing software testing because of costs is very common, with China, the Philippines, and India, being preferred destinations. Requirement gaps can often be non-functional requirements such as testability, scalability, maintainability, performance, and security. Syntax is the specific way we have to write code for a given language.
Integration testing
Load testing is primarily concerned with testing that the system can continue to operate under a specific load, whether that be large quantities of data or a large number of users. The related load testing activity of when performed as a non-functional activity is often referred to as endurance testing. Volume testing is a way to test software functions even when certain components increase radically in size. Stress testing is a way to test reliability under unexpected or rare workloads. Stability testing checks to see if the software can continuously function well in or above an acceptable period.

The use of Given keyword is to put the system in a familiar state before the user starts interacting with the system. However, you can omit writing user interactions in Given steps if Given in the “Precondition” step. Background keyword helps you to add some context to the scenario. It can contain some steps of the scenario, but the only difference is that it should be run before each scenario. Each line called step and starts with keyword and end of the terminals with a stop.
SCL: a language for security testing of network applications
In other words, we can say that security testing is mainly used to define that the data will be safe and endure the software’s working process. In other words, we can say that whenever we are testing an application by using some tools is known as automation testing. Primarily, stress testing is used for critical software, but it can also be used for all types of software applications. While executing the performance testing, we will apply some load on the particular application to check the application’s performance, known as load testing. Here, the load could be less than or equal to the desired load. In other words, we can say that incrementally adding up the modules and test the data flow between the modules is known as Incremental integration testing.
These professionals can take on short-term projects from clients. In the first module of SDET online training, you will be acquainted with the basics of Software Testing. You will learn about the fundamental concepts and terminologies as well as be prepared to answer questions like what is software? This short tutorial will show you how you can benefit from SimpleTester’s Syntax testing that checks for MIB and protocol compliance. Component testing is that in which we test those test objects which are separately testable as a isolated unit without integrating with ot…
The TXL Programming Language
This will involve learning about the different concepts including test flows, test case design, writing and execution of automated test scripts and so on. Additionally, you shall also be acquainted with tools like TestNG Annotations, https://globalcloudteam.com/ Cucumber BDD, Maven, and GITDatabase Fundamentals. Metamorphic testing is a property-based software testing technique, which can be an effective approach for addressing the test oracle problem and test case generation problem.
- Whatever biases the programmers may have had, the tester likely has a different set and may emphasize different areas of functionality.
- Generally, the syntax is tested using two conditions as stated below.Testing the normal condition using the covering set of paths of the syntax graph, for the minimum necessary requirements.
- Background keyword helps you to add some context to the scenario.
- Non-functional testing refers to aspects of the software that may not be related to a specific function or user action, such as scalability or other performance, behavior under certain constraints, or security.
- This means that the number of faults in a software product can be very large and defects that occur infrequently are difficult to find in testing and debugging.
- Functional tests tend to answer the question of “can the user do this” or “does this particular feature work.”
Syntax testing is a powerful, easily automated tool for testing the lexical analyzer and parser of the command processor of command-driven software. Syntax testing needs driver program to be built that automatically sequences through a set of test cases usually stored as data. The last two lines specify a positive and a negative test case. Each test case consists of a name, a code fragment in double square brackets, and a condition which determines what kind of test should be performed and what the expected outcome is . The scenario mentioned above is of a feature called user login. LatchlatchSaves the value of x at the first time latch evaluates in a test step, and subsequently returns the saved value of x.
Destructive testing
Versions of the software, known as beta versions, are released to a limited audience outside of the programming team known as beta testers. The software is released to groups of people so that further testing can ensure the product has few faults or bugs. Beta versions can be made available to the open public to increase the feedback field to a maximal number of future users and to deliver value earlier, for an extended or even indefinite period of time . Once we are successfully implementing the unit testing, we will go integration testing. It is the second level of functional testing, where we test the data flow between dependent modules or interface between two features is called integration testing.
- Published in Software development
10 Types of Consulting fees: Maximize your revenues
My primary focus on helping individuals and couples in their 20s and 30s, many as they start out in their financial lives. I not only want to provide advice to help reach my client’s financial goals, but also to educate them on the about the confusing financial issues they may face. Some clients are more often asking for custom billing plans to help them quantify their return on investment. More and more, clients want consultants to be both highly skilled and up-to-date on the latest technologies. The average IT consulting rate per hour 2022 varies by location and ranges from $20 to $250 or more. For example, in Eastern Europe, the average IT consulting rate is $25-$50/h.
Typically, the amount clients end up paying ranges from a few hundred dollars for a limited financial issue to several thousand dollars for a complex, broad-based financial plan. IT consultant rateper hour are frequently determined by location, company size, experience, and various other factors. For example, the United States has the highest IT consulting rate—$100-$250 per hour, compared to $50/h in Ukraine for the same service.
Thanks for your feedback
In addition, the fee structure for IT consultants varies from one consultant to the next. Some may charge per project, some may charge a tech consultant hourly rate, some may charge a daily rate, and some may work on a monthly retainer. Generally, IT consultants charge 10% of the value of what they’re providing. Our final suggestion is to use this type of fee for ad-hoc projects. Ongoing payment based on hourly rates can be expensive for the client in the long run.
- But you don’t need to spend years learning IT as many IT wizards offer consulting services.
- In the service business, in the bottom line, it is all about fees.
- You can also use communication tools such as project management software, dashboards, or reports to keep track of the scope and document any changes or requests.
- If you are spending any money on materials or transport for the project, you’ll want to include those in your fees.
As a business owner, you want to provide your customers with the best possible services. However, you often don’t have the in-house knowledge or resources needed. When you have a new business, and you’re not quite sure what your focus should be, it can be helpful to hire an IT consultant. They can help you focus on your company’s unique benefits, and they’ll be able to point out opportunities you might have missed. Let’s use the example of hiring an offshore/onshore IT consultant.
What are the Most Popular Expertise Areas of IT Consultants?
Most IT consultants use hourly fees model in order to value their services. They charge for the working hours they have spent in order to carry out the project. It is a demanded option in project development where it is quite challenging to fix the timeline for the completion of a project.
To calculate consulting fees, you need to do some research to find out the current industry rate. Use the current market rate as a benchmark to calculate your rates while considering your experience and expertise. Ultimately, your rate depends on the mutual understanding between you and your client. Most small business owners would love to grow their business. As a result, they eagerly work with a business consultant who specializes in growing start-up businesses and identifying market opportunities. As small business consulting is also in demand, the pricing range will also be higher.
Optimal Practices for Best Offshore Software Development Results
You want to do research to make sure that you aren’t overvaluing or undervaluing your level of experience. Different industries have different rates for projects, so your area of expertise and the scope of the project will influence your pricing model and consultant arrangement. https://www.globalcloudteam.com/ range from $125 to $175 per hour, with project costs ranging from $50,000 to $5 million. We don’t necessarily recommend charging by the hour, but you may want to structure your pricing this way if your consulting work involves meetings and a lot of in-person work. Determining an hourly rate is also an important part of calculating per-project or retainer rates, allowing you a baseline to work from. So whether you want to use the 3 x hourly method for like-for-like rates or the more complicated 52 week, your starting rate is critical to the long-term viability of your consultancy.

The market rate is the average price or range of pricing that clients generally pay for your service. Consider the average market rate in your industry as a small factor in your own pricing. You may be far more experienced than others in average consulting rates by industry the market, meaning you can double the market rate for your services. Conversely, you may be just starting out, and while you may have less experience, you can charge much lower prices – making you much more attractive to new clients.
Main Reasons Why Companies Outsource Software Development
The average cost of IT support services per hour is about $100. You may find specialists ready to work for $50 and those who charge at least $1,000. The pricing varies, so you must evaluate each option from an individual standpoint. Last but of course not least, the consulting charges also rely on the model you choose to pay.
No matter what situation you find yourself in, you have the ability to adjust your fees accordingly. It’s time to create the business you want, delivering value while making a good living. You may find that you have more clients than you can handle. This might suggest that you have priced your services too low and need to increase them. If they were to hire you or someone else to provide the service you are about to provide, they’d be paying for all of those things out of their own pocket . Paying you more to not be an employee actually saves them money in the long run.
Project-Based
That number can be as high or as low as those parties accept. If you’re a business consultant who wants to make $10,000 a day and you find a client who is willing to pay $10,000 a day, you’ve just determined the “value” of your service. If you don’t believe that you have the qualifications, skills, and talents to live up to the promises you’re making, clients will smell your insecurity a mile away.

It can be tricky to balance all of the factors we’ve outlined above, but there are a few steps you can follow to ensure an optimal pricing structure for you and your client. Below we’ll review what influences consultancy fees, how to determine yours, and how to take payments once you’ve started working with clients. The average IT consulting rate varies according to several factors. Generally, companies pay a low figure of $45 per hour to more than $300 per hour when engaging an IT consultant. IT technologies evolve at a pace that companies need help to cope with.
Consultant’s skill and experience
This basically just means the average that consultants are paid based on the services they provide. However, it is very important that you put some thought into dividing them accordingly. Calculate your consulting retainer fee the same way you’d do your project rates—it’s essentially a comprehensive monthly project rather than smaller one-off assignments.
- Published in Software development
The Complete Guide on How To Hire PHP Developers in 2023 Trio Developers
Just start by sharing all information about the project with us to make proper development plan. Once all the project details are gathered, we suggest experienced PHP developers for interviews. Based on your confirmation, we share invoice of hiring PHP developer . Try outsourcing companies, hiring networks, and freelance markets to find PHP engineers to work on your upcoming software project.

You will have to go through thousands of resumes and interviews… When you hire a PHP developer, you are bound to get better ROIs, especially when they utilize PHP to its full potential… Choosing the finest, on the other hand, is critical to your company’s success. Most https://globalcloudteam.com/ PHP frameworks, such as Laravel, Yii, Codeigniter, Zend, Symfony, Kohana, CakePHP, Joomla, and others, should be known to him. Because PHP is so extensively used, there is a significant need to hire PHP programmers, and there are many PHP programmers available for hire.
How to interview PHP developers
The inclusion of these milestones in the roadmap establishes a disciplined approach to development and lessens confusion and hiccups. Clear project goals enable hiring managers to precisely define project scope and budget and find the appropriate developer. Instead of focusing only on your immediate PHP requirements, think about what will be required in a year when hiring a PHP developer.
Here are some reasons to hire PHP developers that might help to end the confusion. Because of this, some PHP programmers make several times as much money as the reported average for this job. So, to hire good PHP developers that can complete your project, you will need to pay at least what developers make on average.
Hire PHP Developers for Dynamic and Interactive Website Development!
If you are looking for a development company to commence your PHP web app development, just trust OrangeMantra. They were simply remarkable in terms of dedication and professionalism. The kind of support they offered was very much appreciated during technical emergencies. We follow agile approach to build bug-free applications meeting user requirements within the set time period.
- You can hire a PHP programmer to cater to your unique business requirements falling in any industry category.
- It is the core language of Facebook as well as the Magento e-commerce platform and WordPress web platform.
- The project’s specifications can be scaled as your business expands.
- Our qualified PHP developers integrate the latest trends to meet your target audience needs and give you a competitive edge.
- You should hire a dedicated PHP developers to keep the web development process in proper shape.
These are PHP developers who you can hire on a per-project basis. They get paid for the whole project or as a milestone or phase is finished. The commands are straightforward and easily correlate with the functions they perform thus encouraging many beginner programmers to start out https://globalcloudteam.com/how-to-hire-a-php-developer/ learning with PHP. Cordenne Brewster is a tech enthusiast whose ardor is best expressed through the written word. With contributions ranging from software development to scaling, Cordenne provides insights to keep the curious and inquisitive informed, well-read, and on-trend.
Advantages of PHP
PHP developers are capable of building dynamic webpage content. They can create graphical interface apps like Microsoft programs that let users interact through icons. Additionally, knowing command-line scripting language, PHP developers get interactive access to the webserver. With the knowledge and expertise PHP developers have, they can create web projects, desktop applications, do command-line scripting and server-side scripting as well. PHP developers are known to be creators of interactive and responsive software projects for Windows, Linux, macOS, RISC OS, and other operating systems.
Since PHP is an open-source language, if there is a vulnerability in the code then others can access the information if they are skilled with getting into the code. This is another area where hiring an experienced and dedicated PHP developer will come in handy, as mistakes with security often come from inexperienced PHP developers. Chances are that you’ve stumbled upon this blog while looking for answers to these and many other critical questions such as “What questions do I ask in a technical interview? ” & “What skills do I check for while hiring a good PHP developer?
Hire PHP Developers in India
The speed, knowledge, expertise, and flexibility is second to none. The Toptal team were as part of tripcents as any in-house team member of tripcents. They contributed and took ownership of the development just like everyone else. While many can legitimately claim to “know” PHP, those who are true experts in the language are capable of producing software that is much more scalable, functional, robust, and maintainable.

- Published in Software development
What is an Embedded System? Definition and FAQs
These are mostly x86-based and often physically small compared to a standard PC, although still quite large compared to most simple (8/16-bit) embedded systems. They may use DOS, FreeBSD, Linux, NetBSD, or an embedded real-time operating system (RTOS) such as MicroC/OS-II, QNX or VxWorks. Examples of properties of typical embedded computers when compared with general-purpose counterparts, are low power consumption, small size, rugged operating ranges, and low per-unit cost. Some systems provide user interface remotely with the help of a serial (e.g. RS-232) or network (e.g. Ethernet) connection.
- The executable running on such a device is typically a monolithic image (all linked together).
- Clearly, the organization and semantics of application contexts change as time progresses and new applications and services are developed.
- Microwave ovens are standalone embedded systems, but they aren’t portable or small to be considered mobile embedded systems.
- Priority is assigned to output generation speed, as real-time embedded systems are often used in mission-critical sectors, such as defense and aerospace, that need important data, well, yesterday.
- The result of the final step of the build process is an absolute binary image that can be directly programmed into a ROM or flash device.
A system on a chip (SoC) contains a complete system – consisting of multiple processors, multipliers, caches, even different types of memory and commonly various peripherals like interfaces for wired or wireless communication on a single chip. SoCs can be implemented as an application-specific integrated circuit (ASIC) or using a field-programmable gate array (FPGA) which typically can be reconfigured. Today, there are billions of embedded system devices used across many industries including medical and industrial equipment, transportation systems, and military equipment. Many consumer devices from digital watches to kitchen appliances and automobiles also feature them.
All Kinds of Operating Systems
An IC-based solution is a hardwired solution that does not contain software and a microprocessor. However, the embedded system solution is more flexible and less expensive, especially when the product needs to be frequently upgraded to accommodate new changes. In response to a new change, for the hardwired solution, a new circuit needs to be designed, constructed, and delivered. In contrast, for the embedded system solution, software patches can be rapidly developed, and the upgrading process can be done over the Internet and may typically take just a few seconds. The importance of embedded systems is continuously increasing considering the breadth of application fields where they are used.
The module vendor will usually provide boot software and make sure there is a selection of operating systems, usually including Linux and some real-time choices. These modules can be manufactured in high volume, by organizations familiar with their specialized testing issues, and combined with much lower volume custom mainboards with application-specific external peripherals. While embedded systems are computing systems, they can range from having no user interface (UI) — for example, on devices designed to perform a single task — to complex graphical user interfaces (GUIs), such as in mobile devices. User interfaces can include buttons, LEDs (light-emitting diodes) and touchscreen sensing. A microcontroller is a single-chip VLSI unit which is also called microcomputer. It contains all the memory and I/O interfaces needed, whereas a general-purpose microprocessor needs additional chips to offered by these necessary functions.
Performance Estimation for Real-Time Distributed Embedded Systems
However, we now see devices such as personal data assistant (PDA)/cell phone hybrids, which are embedded systems designed to be able to do a variety of primary functions. Also, the latest digital TVs include interactive applications that perform a wide variety of general functions unrelated to the “TV” function but just as important, such as e-mail, web browsing, and games. Embedded systems are more limited in hardware and/or software functionality than a PC.
When a task is idle, it calls an idle routine which passes control to another task. The sensor reads external inputs, the converters make that input readable to the processor, and the processor turns that information into useful output for the embedded system. A system is an arrangement where all its component work according to the specific defined rules. It is a method of organizing, working, or performing one or more tasks according to a fixed plan. In contrast, an embedded system is usually sealed, fanless, and ventless, relying on heat sinks for heat dissipation.
Mobile Embedded Systems
Embedded systems are widely used in various purposes, such as commercial, industrial, and military applications. Embedded systems consist of interacting components that are required to deliver a specific functionality under constraints on execution rates and relative time separation of the components. In this article, we model an embedded system using concurrent processes interacting through synchronization. We assume that there are rate constraints on the execution rates of processes imposed by the designer or the environment of the system, where the execution rate of a process is the number of its executions per unit time. We address the problem of computing bounds on the execution rates of processes constituting an embedded system, and propose an interactive rate analysis framework.
D-A converter (A digital-to-analog converter) helps you to convert the digital data fed by the processor to analog data. This measure of the survival probability of the system when the function is critical during the run time. For example, although you can certainly move a washing machine, microwave oven, or dishwasher, you probably don’t consider any of these small or portable as you would a cellphone, laptop, calculator, or other mobile embedded system. POS systems comprise networks of multiple workstations and a server that keeps track of customer transactions, sales revenue, and other customer-related information. As the demand for faster and more efficient high-performance computers increases, the dimensions of the form factors that contain them continue to decrease. An embedded system is a computational system (a computer-like device) set within another device or system—for example, a control unit embedded within a home appliance.
Embedded Systems tutorial provides basic and advanced concepts of Embedded System. Today’s analysts and data scientists are challenged with a growing ecosystem of data sources and warehouses, making big data integration more complex than ever. Your data lives https://doctoralvik.ru/?s=%D0%BA%D0%BE%D0%BA%D0%B0%D0%B2 in many data warehouses and data lakes; it continually flows in through streams or rests as point-in-time files. Regardless of the source, HEAVY.AI easily handles data ingestion of millions of records per second into the iDB open source SQL engine.
- Published in Software development
What is Cloud Security? Understand The 6 Pillars
Therefore, understanding the key differences between on-premise and cloud security will help businesses decide which will improve their security posture, future-proof their spaces, and ultimately fits their unique needs. It’s also important to note that each of the major public cloud providers also have security companies list their own native cloud security controls and services that organizations can enable. Understanding your responsibilities on these platforms under the shared responsibility model of cloud security is critically important. VMware is a leading provider of virtualization and cloud computing solutions.
Some access control providers like Openpath also have a remote unlock feature, so admins can open the door for people without having to be onsite. This paper describes security best practices for protecting sensitive data in the public cloud, and explains concepts such as BYOK, HYOK, Bring Your Own Encryption , key brokering and Root of https://globalcloudteam.com/ Trust . Software as a Service Consists of applications hosted by a third party and usually delivered as software services over a web browser that is accessed on the client’s side. While SaaS eliminates the need to deploy and manage applications on end-user devices, potentially any employee can access web services and download content.
Security Research & Services
Illumio Core is a CWPP solution that emphasizes preventing the lateral movement of data. It allows for control over an organization’s data hubs and cloud environments to monitor and gain insight into application interactions within cloud environments. Cato’s SASE tool is a cloud-based security tool featuring a combination of SD-WAN, a network security solution, and support for a variety of cloud applications and mobile devices.

The software-as-a-service revolution has added to this trend, making the cloud a go-to environment for most productivity tasks. Zero Trust, for example, promotes a least privilege governance strategy whereby users are only given access to the resources they need to perform their duties. Similarly, it calls upon developers to ensure that web-facing applications are properly secured. Was first introduced in 2010 by John Kindervag who, at that time, was a senior Forrester Research analyst. The basic principle of Zero Trust in cloud security is not to automatically trust anyone or anything within or outside of the network—and verify (i.e., authorize, inspect and secure) everything. XDR shines in its ability to combine data from cloud environments with data from on-premises systems and other distributed systems, such as IoT.
Why is cloud security important?
While having all data stored on locally hosted servers may seem like the safer bet to reduce cloud security vulnerabilities, on-premise security systems are not necessarily more secure than their cloud-based counterparts. The fact remains that even on-premise solutions are subject to breaches, with insecure VPN networks and human error both contributing to many recent security incidents. Limited customization options—When it comes to customized security, the options are infinite with on-premise security solutions. Cloud-based systems offer more limited choices, which may work for small businesses that do not require complex IT infrastructure. For larger organizations, customization options might be the deciding factor in choosing between on-prem and cloud-based.
Risk databases for cloud providers are available to expedite the assessment process. Four cloud security solutions include cloud data visibility, control over cloud data, access to cloud data and applications, and compliance. With many organizations currently reevaluating their spaces, budgets and work policies, security continues to play a vital role in every industry.
CloudFest 2023 Recap: The Resilient Cloud
Compatibility and coverage are often the make-or-break factors when choosing a cloud security platform. For example, if your assets primarily reside in an AWS environment, you need security software that’s purpose-built for AWS. For multi-cloud environments, the platform must be certified to function with all major public clouds like AWS, Microsoft Azure, and Google. Or, if you are heavily invested in private cloud servers, the cloud security software must be able to adapt.

Synopsys’ Cloud Security Maturity Plan prepares a comprehensive roadmap documenting recommendations to improve cloud security strategy and aid your software security initiative . The MAP recommends top security goals and outlines strategies to meet them by evaluating your current resources. Dynamic Application Security Testing detects security vulnerabilities and reduces the risk of a data breach. After testing, we explain your results in detail and collaborate with you on a plan to effectively move forward.
Vulnerability monitoring and intrusion detection
Cloud security solutions are software tools that secure cloud architectures and identities, identify and remediate vulnerabilities, prevent threats, and help respond to incidents when they occur. The “cloud” or, more specifically, “cloud computing” refers to the process of accessing resources, software, and databases over the Internet and outside the confines of local hardware restrictions. This technology gives organizations flexibility when scaling their operations by offloading a portion, or majority, of their infrastructure management to third-party hosting providers.
User access can be from any location or device, including bring-your-own-device technology. In addition, privileged access by cloud provider personnel could bypass your own security controls. Features include access control, threat protection, data security, security monitoring, and acceptable usage control, all implemented through web-based and API-based integrations. However, successful cloud adoption is dependent on putting in place adequate countermeasures to defend against modern-day cyberattacks.
Centralized Cloud Authentication and Access Management
Also, cloud security is an evolving challenge which can be addressed only if the technologies and tools are structured to grow along with it. If you want to know what personal data we have about you, you can ask us for details of that personal data and for a copy of it . For more information about our use of your personal data or exercising your rights as outlined above, please contact us using the details provided in Section 10. PowerDMARC as an email authentication SaaS platform that allows you to verify the sender of an email and ensure that they are who they say they are. This can be important if your company deals with sensitive information, as it helps reduce the likelihood of phishing or spoofing attempts.
- It allows organizations unified cloud management and several advanced security controls that cover both the cloud and on-campus network activities.
- Cloud security can also scale during high traffic periods, providing more security when you upgrade your cloud solution and scaling down when traffic decreases.
- It is time for companies to deploy a new set of solutions to provide a Secure Service Edge .
- Other features, like identity management, layer seven level security, and API protection as well as a sleek reporting infrastructure make this truly an all-in-one cloud security solution.
- A Certified Information Systems Security Professional , Wagner is adept in security architecture/analysis, cyber threat detection, risk management, incident response, and contingency planning.
- Given that so many companies now use a multicloud strategy, a solution must have the ability to work in a multicloud scenario, with diverse types of deployments.
- Published in Software development
Security, Identity, and Compliance
Content
- Why the Cloud Offers Better Protection Than Appliances
- Skyhigh Security Named a Visionary in the 2023 Gartner® Magic Quadrant™ for Security Service Edge
- Get started with Oracle Security
- Gartner® Critical Capabilities for Security Service Edge
- Data encryption
- What is Cloud Computing Security?
- What does cloud computing security do?
Thales Partner Ecosystem includes several programs that recognize, rewards, supports and collaborates to help accelerate your revenue and differentiate your business. Security architects are implementing comprehensive information https://globalcloudteam.com/ risk management strategies that include integrated Hardware Security Modules . The analyst now knows what systems and users were involved, can view their activities, and consult with or apply playbooks for remediation.

Regardless of how it happens, the implications of data breach are the same – a potential fine for non-compliance and a damaging loss of reputation. Cloud workload protection technologies work with both cloud infrastructure as well as virtual machines, providing monitoring and threat prevention features. Unfortunately, malicious actors realize the value of cloud-based targets and increasingly probe them for exploits.
Why the Cloud Offers Better Protection Than Appliances
SafeNet Trusted Access ensures that only validated and authorized users can access sensitive data and apps in the cloud. Read about how we prevent data breaches and help organizations comply with regulations to secure access to cloud properties across IaaS, PaaS and SaaS. SSE technology enables organizations to implement security policies and support their employees anytime, anywhere using a cloud-centric approach.
While cloud compliance solutions are passive tools that can notify about violations, provide remediation instructions, and generate detailed reports and audits. Cloud security is gaining importance at many organizations, as cloud computing becomes mainstream. Most organizations use cloud infrastructure or services, whether software as a service , platform as a service or infrastructure as a service , and each of these deployment models has its own, complex security considerations.
Skyhigh Security Named a Visionary in the 2023 Gartner® Magic Quadrant™ for Security Service Edge
These tools are the most mature and established in cloud security and comparatively broader than other cloud security tool types. Radware provides smart, comprehensive application protection that gives organizations visibility and lets them take back control of their protections. Protect your workforce from the latest threats and data loss while accessing the web and cloud applications. Threat protection with data-centric visibility and control over your cloud apps, without compromising on security. Over the past decade, cloud adoption has seen explosive growth at both consumer and enterprise level, and it is easy to see why.
It’s important to identify the workloads you need to protect and ensure that the cloud security solution provides protection features that are appropriate for the given workload. Cloud security solutions suites may include capabilities from both cloud workload and CASB technologies, to help provide a comprehensive set of features that secure cloud access and deployments. While enterprises can insist on a private cloud — the internet equivalent of owning your own office building or campus — individuals and smaller businesses must manage with public cloud services.
Get started with Oracle Security
Cloud environments are different from traditional networks and continually change, which means any approach to cloud-based security must be adaptable. Hybrid Cloud– where data and applications move between both public and private clouds, allowing organizations to reap the benefits from both environments. Check Point’s CloudGuard platform has multiple capabilities to help organizations maintain consistent security companies list security policies and protect different types of cloud deployments. The platform encompasses security for both IaaS as well as SaaS cloud use cases. Run Enterprise Apps Anywhere Run enterprise apps and platform services at scale across public and telco clouds, data centers and edge environments. Segmentation of services can help an organization control how their data is accessed and stored.
- Security architects are implementing comprehensive information risk management strategies that include integrated Hardware Security Modules .
- While connecting to all those clouds is easy, managing the different environments can get complicated quickly.
- Use cases include next-generation networking, security functionality, and observability.
- Alternatively, a power outage could affect the data center where your data is stored, possibly with permanent data loss.
CCSP is a role that was created to help standardize the knowledge and skills needed to ensure security in the cloud. This certification was developed by ² and the Cloud Security Alliance , two non-profit organizations dedicated to cloud computing security. Cloud native applications commonly include open source components, which may include a large number of dependent packages. It is important to scan these components and their dependencies for open source vulnerabilities. This must be automated, and integrated into deployment processes, so that every component deployed in the cloud native environment is verified to be free of security vulnerabilities.
Gartner® Critical Capabilities for Security Service Edge
Multi-Cloud made easy with a portfolio of cross-cloud services designed to build, operate, secure, and access applications on any cloud. So, whether you are an individual user, SMB user, or even Enterprise level cloud user — it is important to make sure that your network and devices are as secure as possible. Remember that many of these commonly available cloud storage services don’t encrypt data. If you want to keep your data secure through encryption, you will need to use encryption software to do it yourself before you upload the data. You will then have to give your clients a key, or they won’t be able to read the files. Find out more about what cloud security is, the main types of cloud environments you’ll need security for, the importance of cloud security, and its primary benefits.

Cloud IAM services Navigate your journey to a successful cloud identity and access management program migration. Integrate native cloud security controls, implement secure-by-design methodology and establish security orchestration and automation to define and enforce your enterprise cloud security program. This has thrust cloud security into the spotlight, along with the necessity for enterprises and public organizations to protect their cloud activities. Cloud network reliance and usage are spiking to record levels as day-to-day business activity becomes increasingly dependent on a growing number of IaaS, PaaS, and SaaS cloud services. C3M Access Control is a CIEM solution that manages and enforces access privileges across the cloud infrastructure to prevent over-provisioned access and potential insider threats. Cisco’s Systems Cloudlock offers an enterprise-focused CASB solution to safely transfer and manage users, data, and apps on the cloud.
Data encryption
Despite cloud providers taking many security roles from clients, they do not manage everything. This leaves even non-technical users with the duty to self-educate on cloud security. Identity and access management pertains to the accessibility privileges offered to user accounts. Access controls are pivotal to restrict users — both legitimate and malicious — from entering and compromising sensitive data and systems.
- Published in Software development
Where to Hire Blockchain Developers in 2023
As a result, businesses can save on potential losses to financial hacks or embezzlement. So, for example, logistics businesses can conduct their monitoring on the Blockchain to reduce chances of http://investfondspb.ru/Glava%204/Index19.html loss. Help investors trust your Blockchain idea/product by offering them a robust MVP. Your business can demonstrate the feasibility of your Blockchain product with a representative MVP app.
- For example, our Blockchain experts have implemented multi-cryptocurrency as a payment option in many web and mobile apps.
- There is also a 7 days money-back guarantee after the project’s kick-off.
- For example, they have much better transaction throughput, additional security layers, and specific consensus algorithms.
- These numbers are subject to change due to the evolving nature of the industry and the high demand for these skills.
- For the last four years, he’s been working as a member of a rapid prototyping team at Daimler AG, focusing on blockchain projects.
He also has experience in building startups and designing products, as he is a co-founder of DoxyChain, a blockchain-based document management system. David is a senior software engineering generalist with blockchain and security experience. With two years of management training and strong communication skills, he excels at bridging business requirements with modern technology. David’s current passion is building on his experience as a leader to maximize team effectiveness through industry best practices. Our blockchain developers are skilled and experienced in designing and developing robust decentralized apps (dApps).
What Blockchain development services does Riseup Labs offer?
Riseup Labs ensures every client is kept informed via their preferred communication channels like Zoom, Skype, or email. Thus, you can hire Blockchain experts with effective communication. Define your project’s technological stack, and we’ll match you with highly skilled developers. Transactions conducted in the Blockchain are stored in chronological order. Thus, the Blockchain can verify that the operations are accurate – making each transaction unchangeable. So, hire Blockchain programmers to develop trustworthy apps for your business.
Find the most talented Blockchain development experts on Fiverr to bring your ideas to life. This kind of consensus is the agreement among a distributed system’s nodes about the state of the system. It is a difficult computer science problem without a general solution, having been solved only for specific use cases, like bitcoin. It is the only block which does not contain a hash referring to a previous block.
Streamline Hiring Process
Hire the candidate you find suitable, by using the simple contracting processes offered by Guru. Depending on your screening process, you can get quality blockchain programmers. Arc manages the payroll, benefits, and other compliance activities for all hires.
DApps (sometimes spelled also as dApps) itself is short for distributed application — one leveraging the full potential of blockchain and running always on numerous devices. Such apps are powered by the concept of smart contracts responsible for the automation of transactions between the two sides participating in them. Build a democratic and transparent application on the public Blockchain.
Onsite Dedicated Team
Top companies work with Toptal blockchain engineers to launch ICOs, write smart contracts, create Dapps, and more. Asking the right questions and giving insightful coding tasks is the only way to hire a blockchain developer who will deliver amazing results. If you are not such an expert yourself, you should be assisted by someone who will provide you with the technical context for the interview. Hire Blockchain Developers from Riseup Labs for the full spectrum of Blockchain development services. You can engage skilled Blockchain experts to build digital cash systems, smart contracts, Blockchain wallets, cryptocurrencies, and more. So, hire remote Blockchain developers from Riseup Labs’ pool of experts to bring high performance and scalability to your business.
These numbers are subject to change due to the evolving nature of the industry and the high demand for these skills. That can be a great idea since you get access to a global pool of talent. Many skilled developers in the blockchain industry work remotely.
- Published in Software development
Quality assurance vs Quality Control: Know the Differences
Content
Quality assurance covers the necessary grounds for ensuring that quality is achieved in production. The many roles of the quality assurance team are to make this realizable. Quality Assurance is done in the software development life cycle, whereas Quality Control is done in the software testing life cycle.
The focus of QA will be on the quality of the verification process and preventing defects while the QC will focus on the entire end product and fixing flaws. The testing process cannot be subjected to one model as they are various kinds of tests that a product undergoes. For example, Functional testing will only check for conformance to requirements. After resolving raised issues, a series of regression and sanity tests are required to ensure the final quality product.
Continuous Improvement
Purchasing controls, production and process controls, and training guidelines for staff all live in your QMS and will need to be continuously updated in response to any defects you discover. Internal audits are also an important aspect of quality assurance, and any FDA audit will require that you present the findings of any internal audits you have conducted. There should be several QA and QC steps in place in order to release a high-quality product. QA activities guide organizations on how to do this, while QC helps organizations to ensure their finished product complies with all the necessary requirements. The QMS is the responsibility of the Quality department—specifically, the leadership of the team—while QA activities consist of standards for training, documentation, and review throughout the team. They represent an organization-wide effort whereby each team member must follow the defined SOPs.
It is a Japanese management philosophy used for improving productivity in a methodical manner. Kaizen recommends the involvement of all the employees in order to improve operations continuously. Appropriate methodology and tools in identifying, measuring, and responding to issues of non-conformance are used. Detecting the weak position and the cause of the trouble in the weak position by checking the product design.
Chapter 8: Benefits of QA and QC
Quality improvement is a formal approach to analyse the feedback received from the quality control team. In this process efforts are put systematically to identify any room of improvements in the existing standards and procedures. The target is to improve the process that establish the standards of quality in the organization.
- An iterative process between QA and QC allows for continuous quality improvement.
- For a person who has nothing to do with software development and testing, quality assurance and quality control seem to be the same thing.
- Let’s have a closer look at this segment of the dynamic testing process.
- Even though the concept of quality has existed from early times, the study and definition of quality have been given prominence only in the last century.
- There are many ways that this is accomplished, such as with ISO 9000 or a model such as Capability Maturity Model Integration .
Enjoy all these benefits by adopting Quality Control in your industry. Data gathering and management designed for MedTech clinical trials and operations. Experience the #1 QMS software for medical device companies first-hand. The most commonly-used graph for showing frequency distributions, or how often each different value in a set of data occurs. Quality assurance vs. Quality control “It took too long to find things, and then at a point in time when you wanted to update the procedures, you never knew how many copies were flying around and where they were at,” Austin laments. The Pareto diagram was named after the founder Vilfredo Pareto who observed that a small percentage of a group will usually have the largest impact.
Advantages of Quality Assurance
Many product owners doubt its value as a separate process, putting their businesses and products at stake while trying to save an extra penny. In Agile software development, the testing typically represents an iterative process. While the levels generally refer to the complete product, they can also be applied to every added feature.
These checks may be performed after meeting certain production outputs, such as 10,000 units, or as part of completely randomized audits. By using QC to review and standardize production methods, you can ensure each product meets the same standards each and every time. Without QC, you might not find out there is a problem with your product until consumers complain or demand refunds. Quality control focuses on finding defects or anomalies in the deliverables and checking if the defined requirements are the right requirements.
The Difference Between Quality Assurance and Quality Control
So if you’re a software tester or quality assurance engineer, TestSigma is perfect for you! Get started and see how it can improve https://globalcloudteam.com/ your software testing process and product quality. In theory, quality control can be achieved with minimal testing.

Remember, QA tends to be more big picture and longer term than QC. We often use the terms “quality control” and “quality assurance” interchangeably, but they have different meanings and strategies. Facility ManagementIncrease asset lifespan and manage standard operating procedures.
Proactive vs. reactive
On the other hand, Quality Control is there to detect a number of possible hazards caused by microbiological growth, chemical or physical contamination. Both aspects bind together will improve and ensure safe food products. Start implementing these techniques and improve the quality assurance and quality control process in your organization. Let us know about your success with those in the comment section below. I hope this article finally resolves the confusion surrounding quality assurance vs quality control. Now you can communicate confidently while using the terms and know what exactly you or the client is referring to.
- Published in Software development
- 1
- 2


